-
Products The SecurEnvoy Solutions >
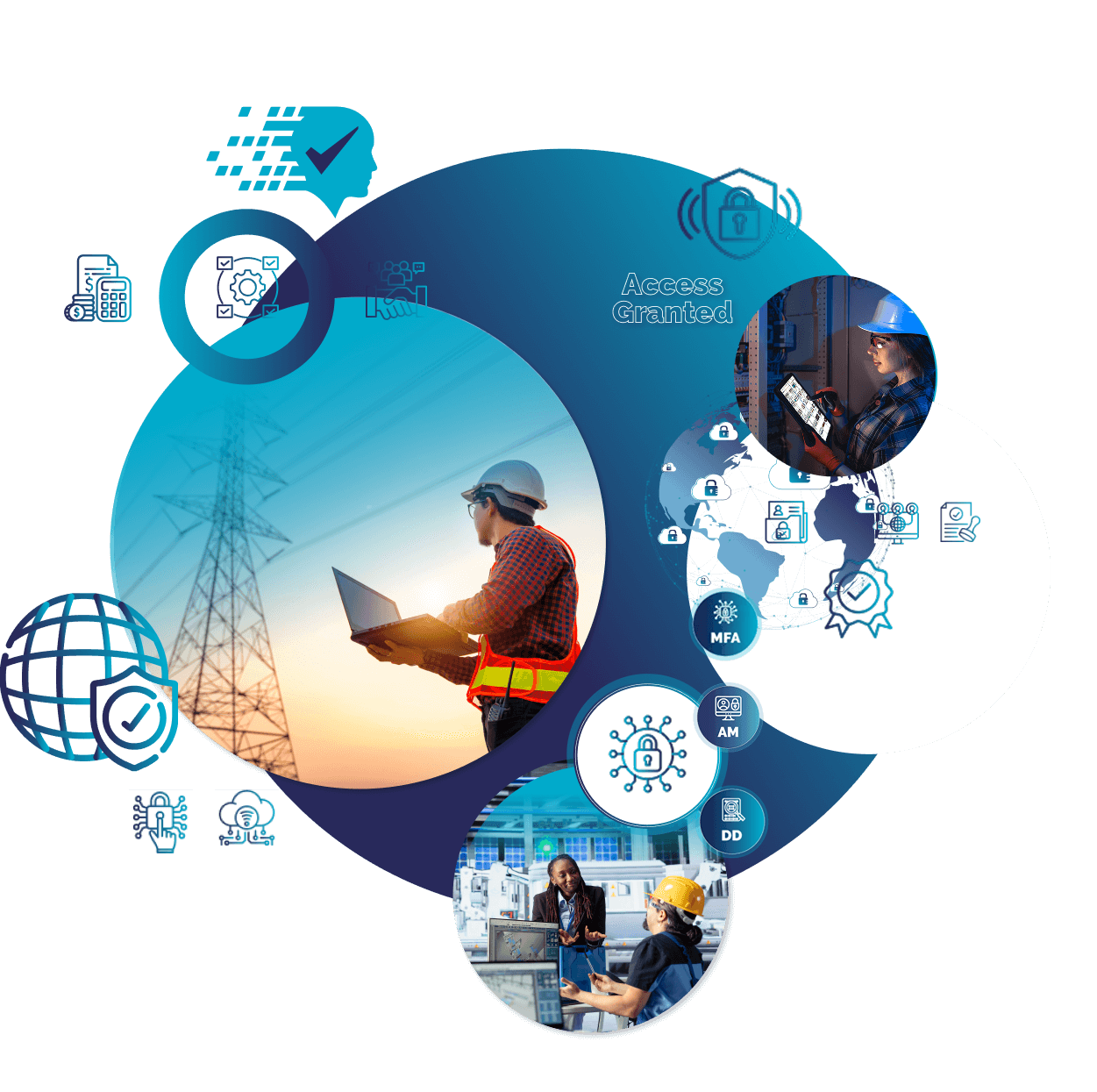
Allowing organisations to provide verifiable trust in every activity they perform.
- Access Management >
Quick to deploy with simple administration and an intuitive user interface.
- Multi-Factor Authentication (MFA) >
Flexible and effective authentication across all platforms, device and authentication method.
- Data Discovery (DD) >
Effective and easy-to-use for data visibility across your entire digital estate.
- Access Management >
-
Solutions Industry Sector >
SecurEnvoy works all major vertical sectors – protecting business assets, users, data and devices.
-
Resources Useful resources >
Effectively learn about the SecurEnvoy Solutions – considering the wider industry picture and current day challenges and threats.
- Latest enablement videos >
Our vision and platform introductions – quick snapshot enablement.
- Case studies >
With 1000’s of global customers we are fortunate to have some great case studies
- Latest documents >
Our research and discussion documents around cyber security and authentication.
- Integration Guides >
See our support area for many other useful technical resources
- Latest webinars >
Live and recorded –
use them how it suits you. - Industry enabling blog >
Covering industry challenges, threats and technologies. Considering solutions and techniques to progress effectively
- Latest enablement videos >
-
Partnerships Become a Partner >
SecurEnvoy engages with focused partners across the globe. Effectively delivering customer solutions and ensuring we are connected to valued technology partners
- Technology partner integrations >
Our Solutions integrate with many leading technology platforms and companies
- Find a SecurEnvoy partner >
Locate a qualified SecurEnvoy partner that can deliver effectively to your business
- How to become a partner >
Nearly 20 years of embracing partnership.
- Webinars for partners >
- Partner Portal >
Access your partner portal resources
- Deal registration >
For SecurEnvoy channel partners
- Technology partner integrations >
-
Support SecurEnvoy support >
Our support is built around our customers, engaging and supporting effectively is vital to our business. Our customer support feedback receives 4.2/5 – with 80% not needing any support, but do not hesitate to contact us!
-
Company About SecurEnvoy >
Over 20 years of leading innovation. SecurEnvoy continues to develop and provide reliable cybersecurity solutions, supporting secure digital transformation across industries. Part of the Shearwater Group plc
- Join SecurEnvoy >
Be part of the SecurEnvoy Team where innovation and customers are our focus
- Press and Events >
The latest press releases, coverage and events.
- Industry enabling blog >
Covering industry challenges, threats and technologies. Considering solutions and techniques to progress effectively.
Latest blogs:
+ What the Defence Cyber Certification means for the defence supply chain (and where to start) >
+ How the government’s “Lock the Door” campaign helps meet Cyber Essentials requirements >
- Join SecurEnvoy >