-
Productos La solución de accesos Zero Trust de SecurEnvoy >
Permite a las organizaciones proporcionar una confianza verificable en todas las actividades que realizan.
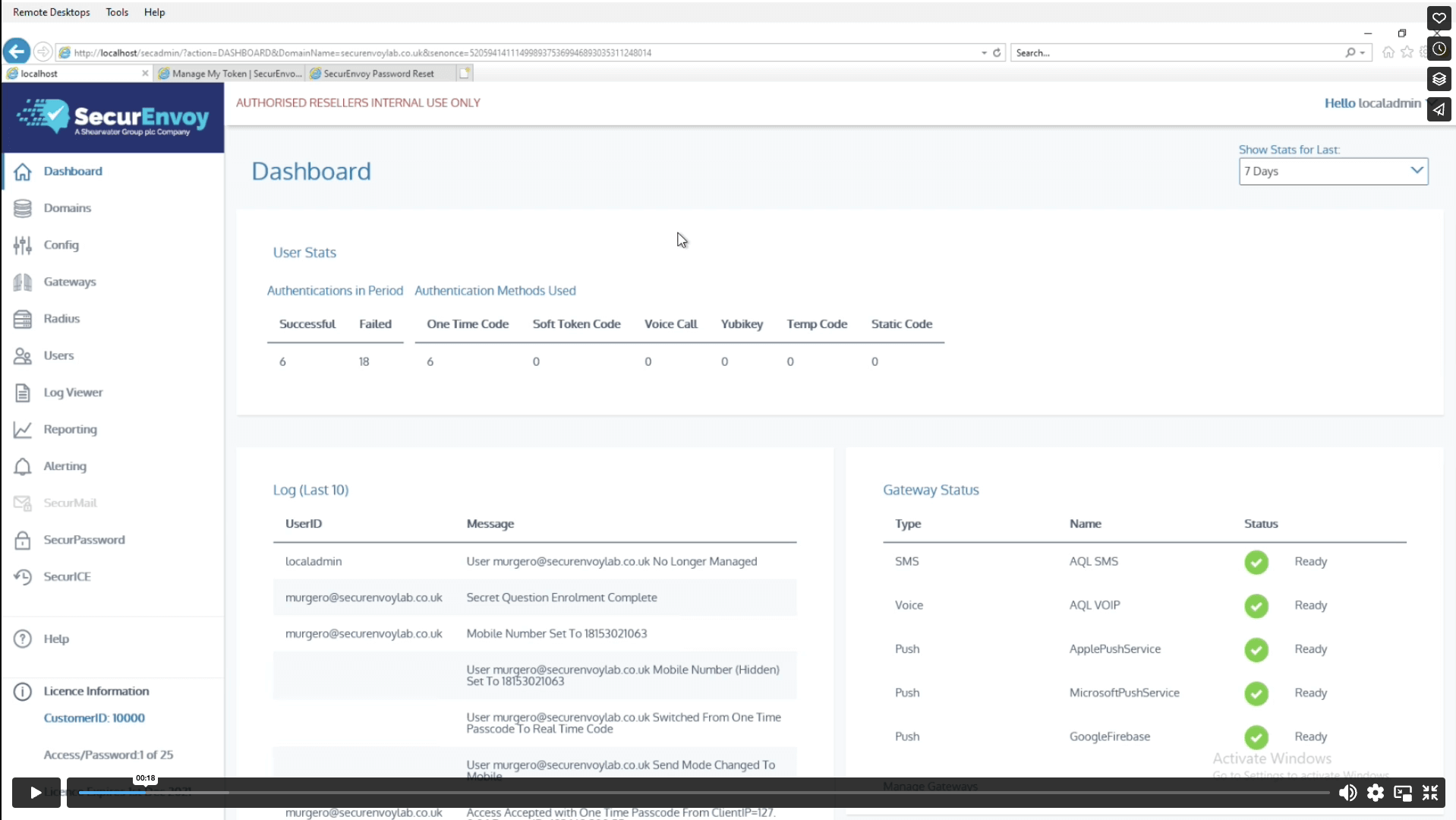
- Gestión de accesos >
Gestión de accesos rápida de implementar con una administración sencilla y una interfaz de usuario intuitiva.
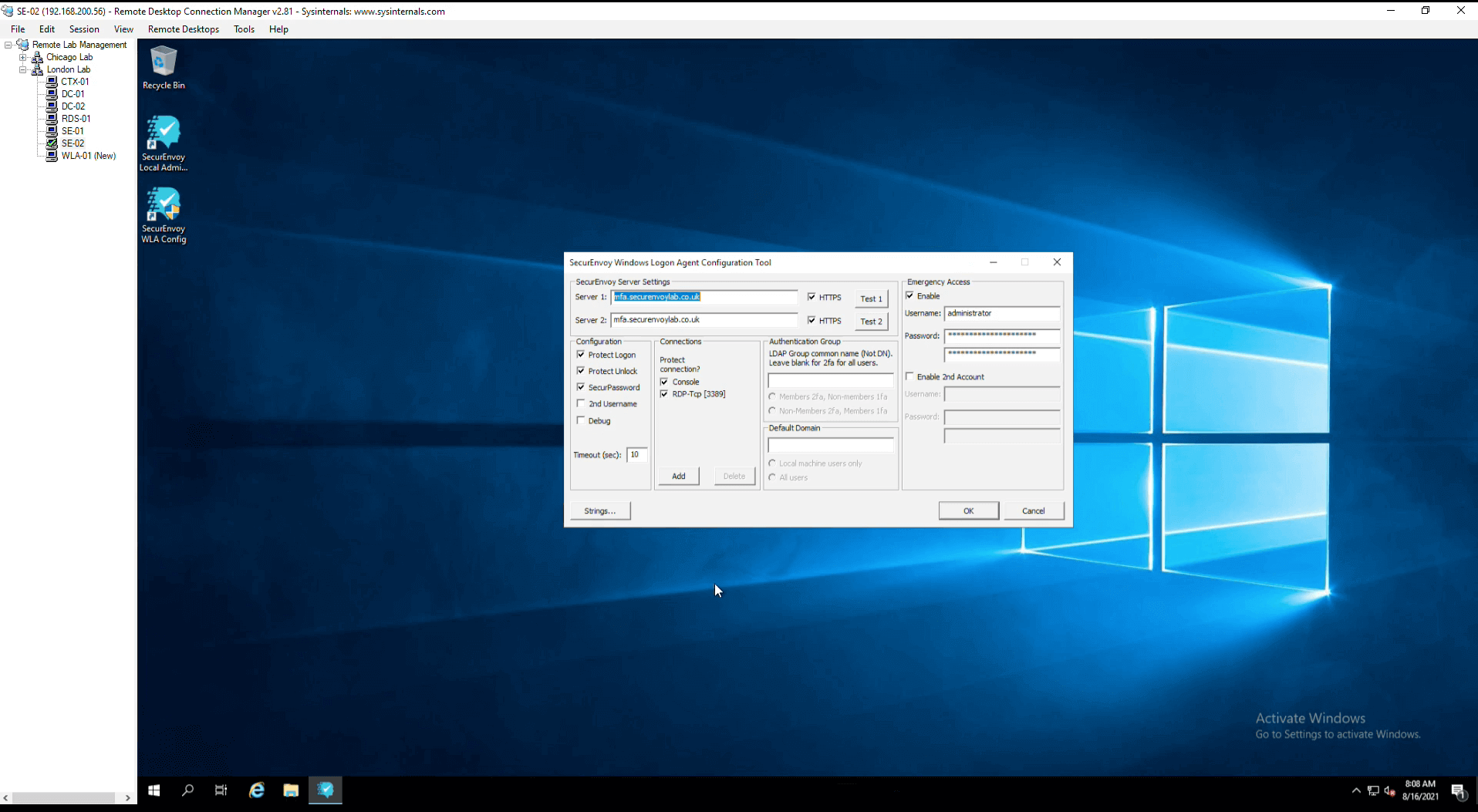
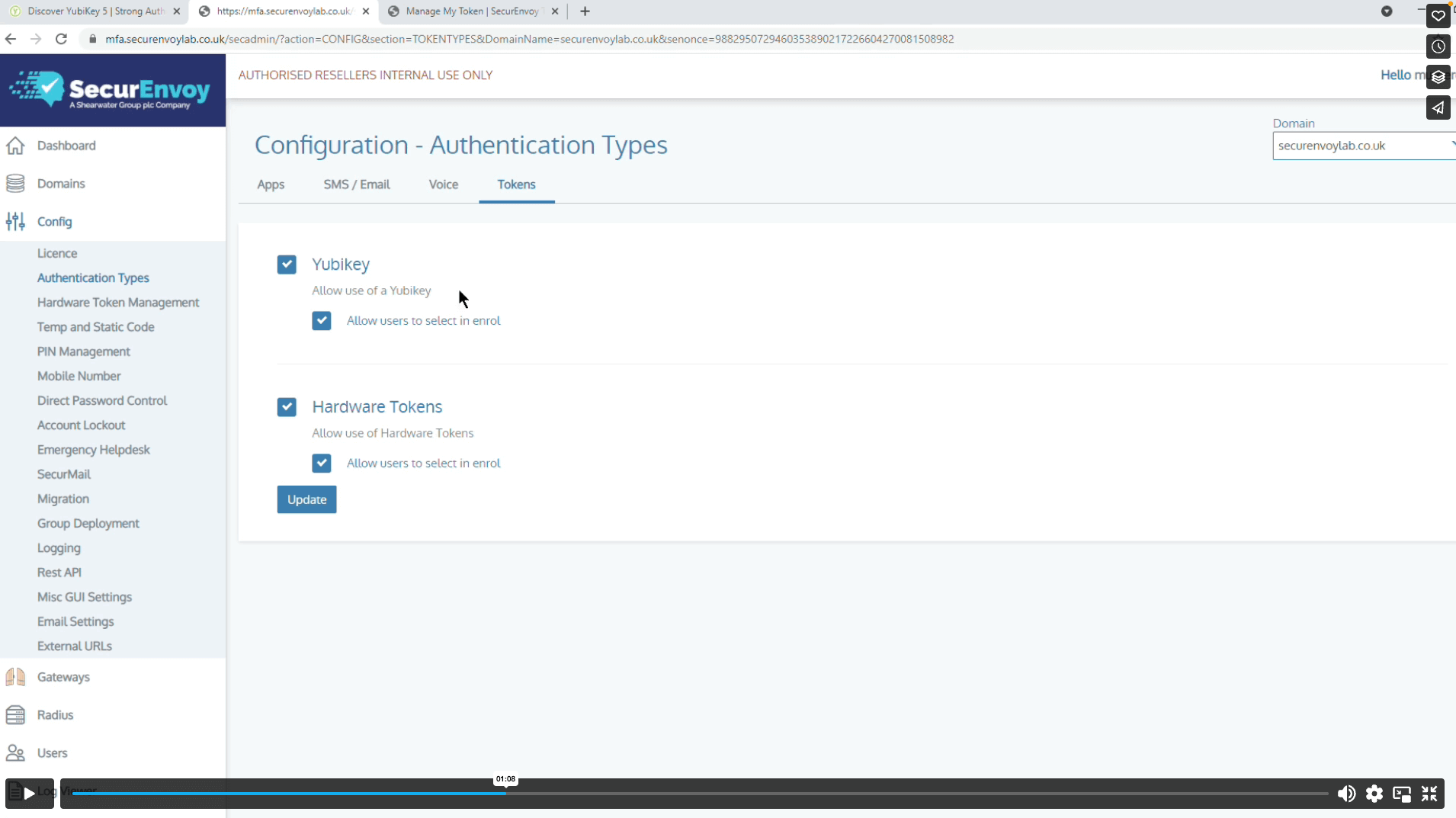
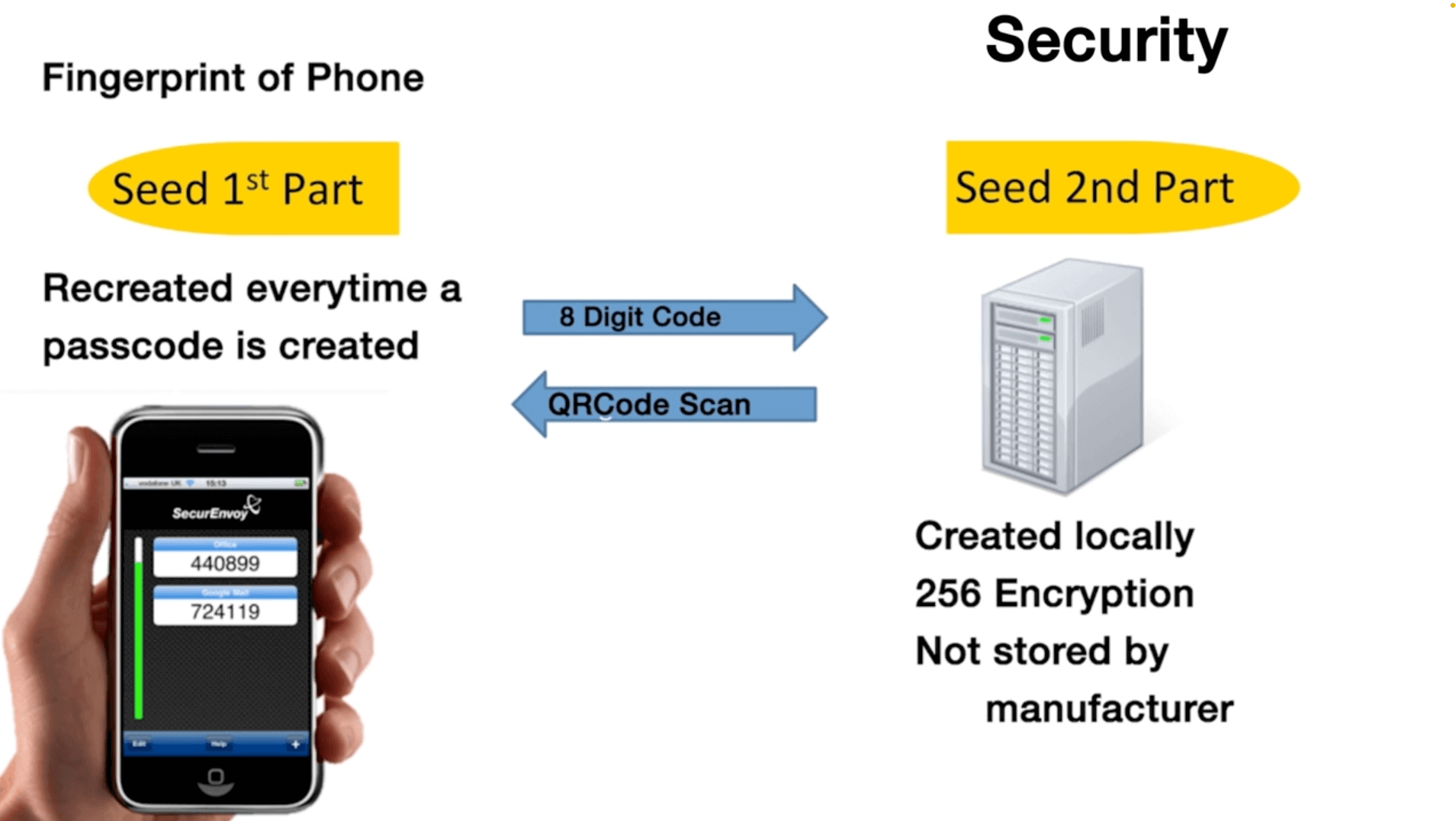
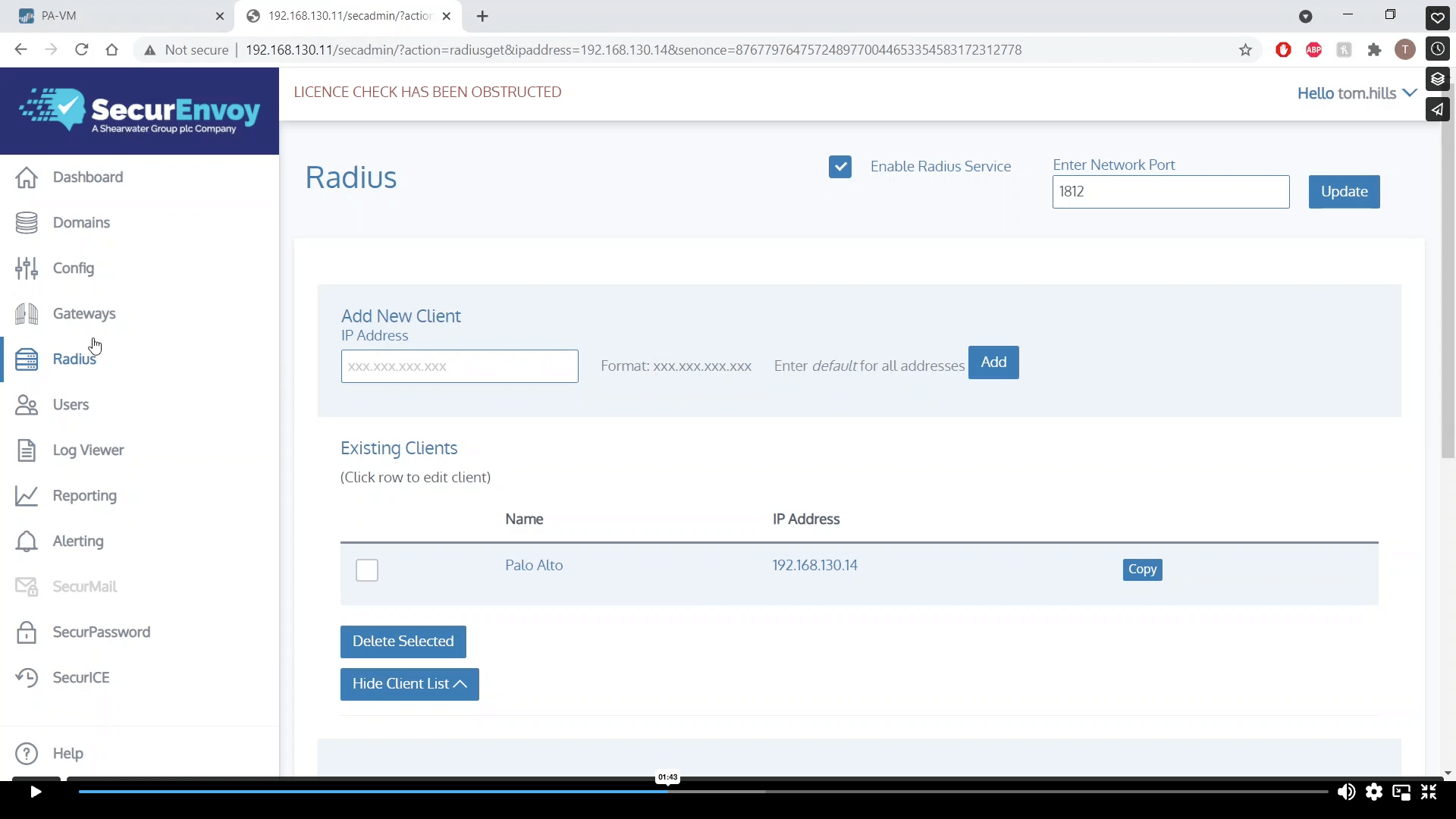
- Autenticación Multi Factor (MFA) >
Autenticación flexible y eficaz en todas las plataformas, todos los dispositivos y con todos los métodos de autenticación.
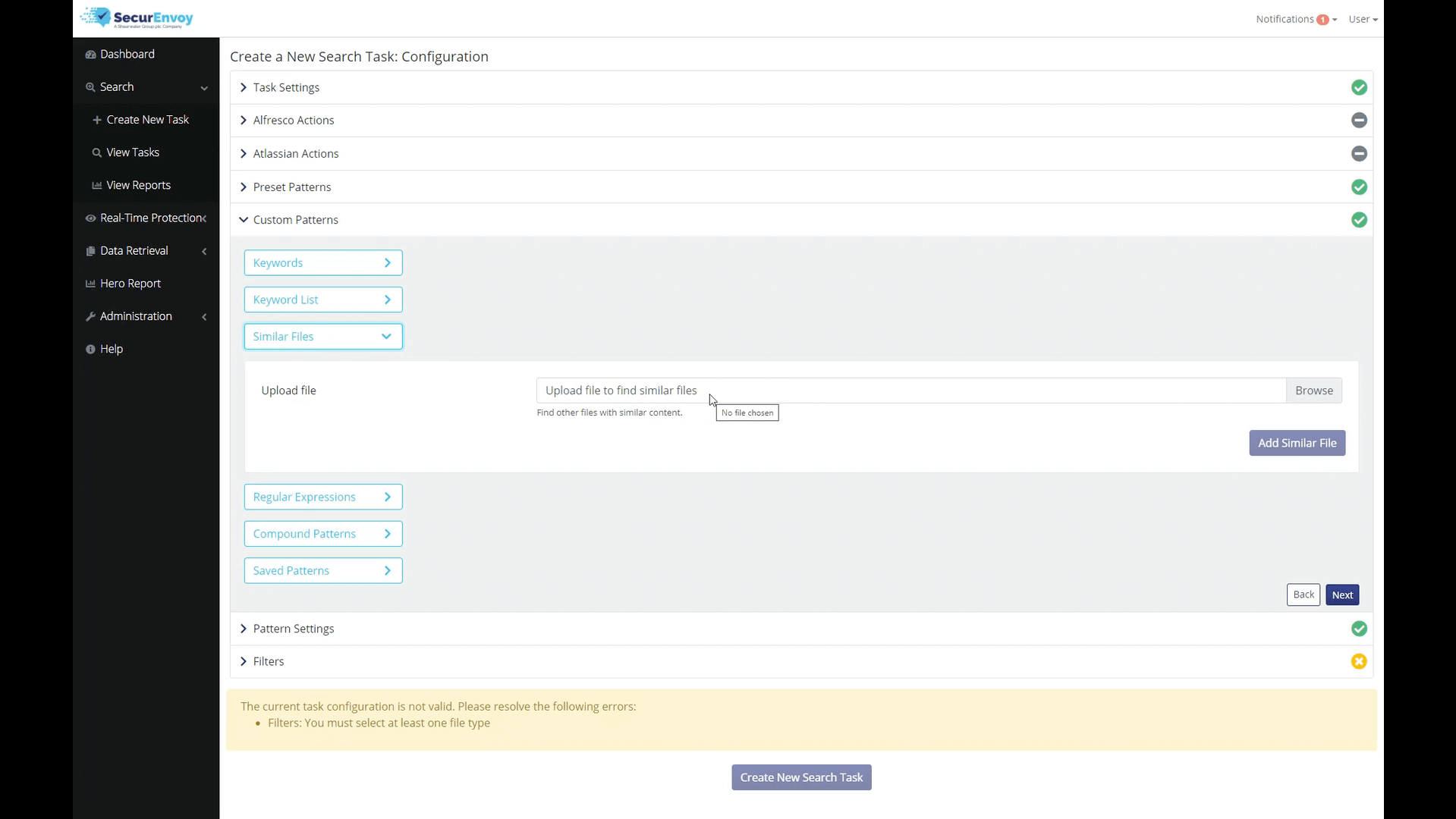
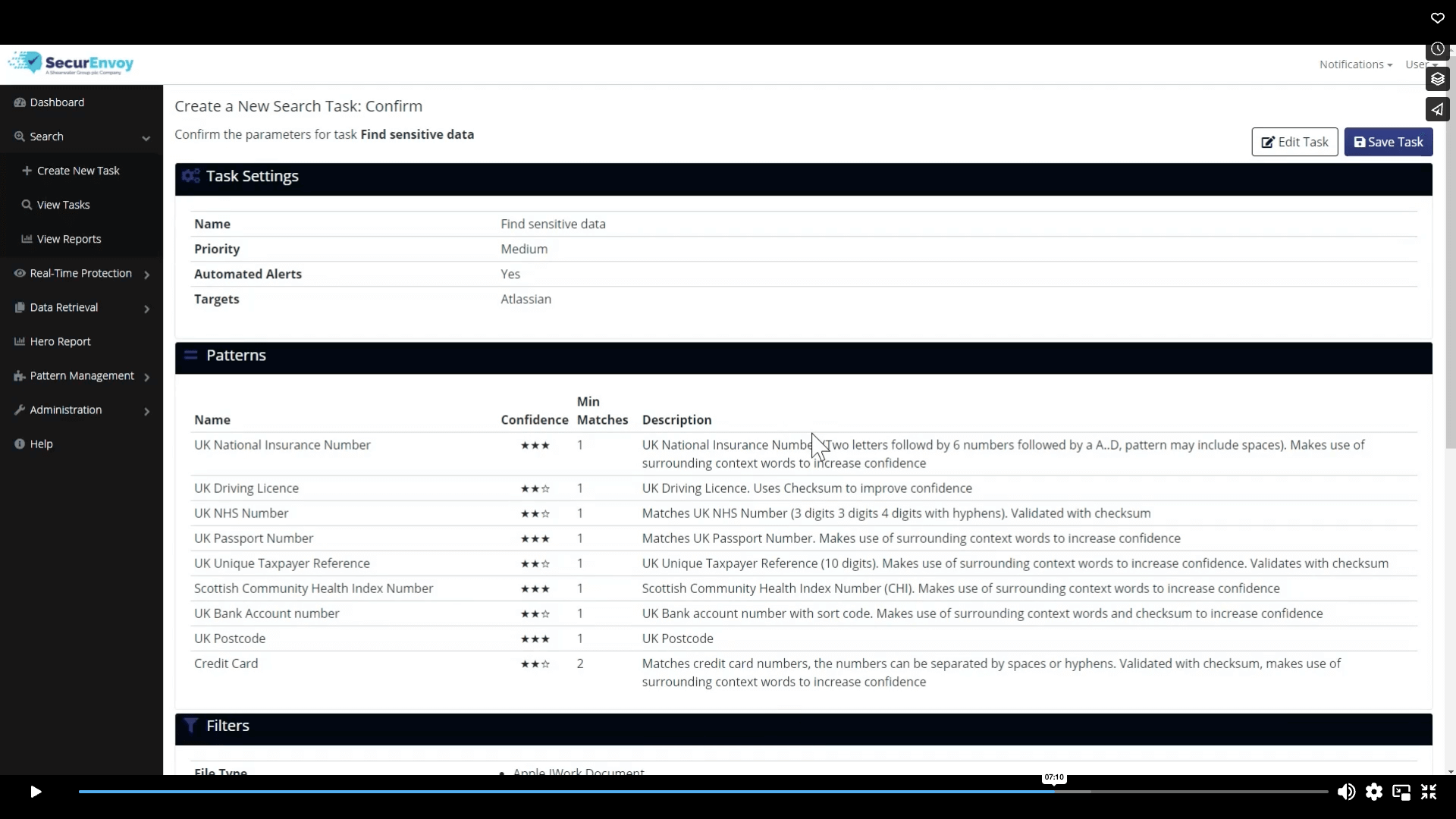
- Data Discovery (DD) >
Descubrimiento de datos eficaz y fácil de usar para la visibilidad de los datos en todo su patrimonio digital.
- Gestión de accesos >
-
Soluciones Sectores industriales >
SecurEnvoy trabaja con la mayoría de los sectores verticales – protegiendo los activos de la compañía, usuarios, datos y dispositivos
-
Recursos Recursos útiles >
Aprender en profundidad las plataformas SecureIdentity & Protection Suite , teniendo en cuenta una perspectiva más amplia del mercado y las amenazas y desafíos actuales.
- Nuevos vídeos >
Nuestra visión e introducciones a nuestras plataformas – vista rápida
- Estudio monográfico >
Con más de 1000 clientes a nivel global, poseemos unos estudios monográficos excelentes
- Informes oficiales recientes >
Nuestros informes oficiales en investigación y discusión sobre ciberseguridad y autenticación.
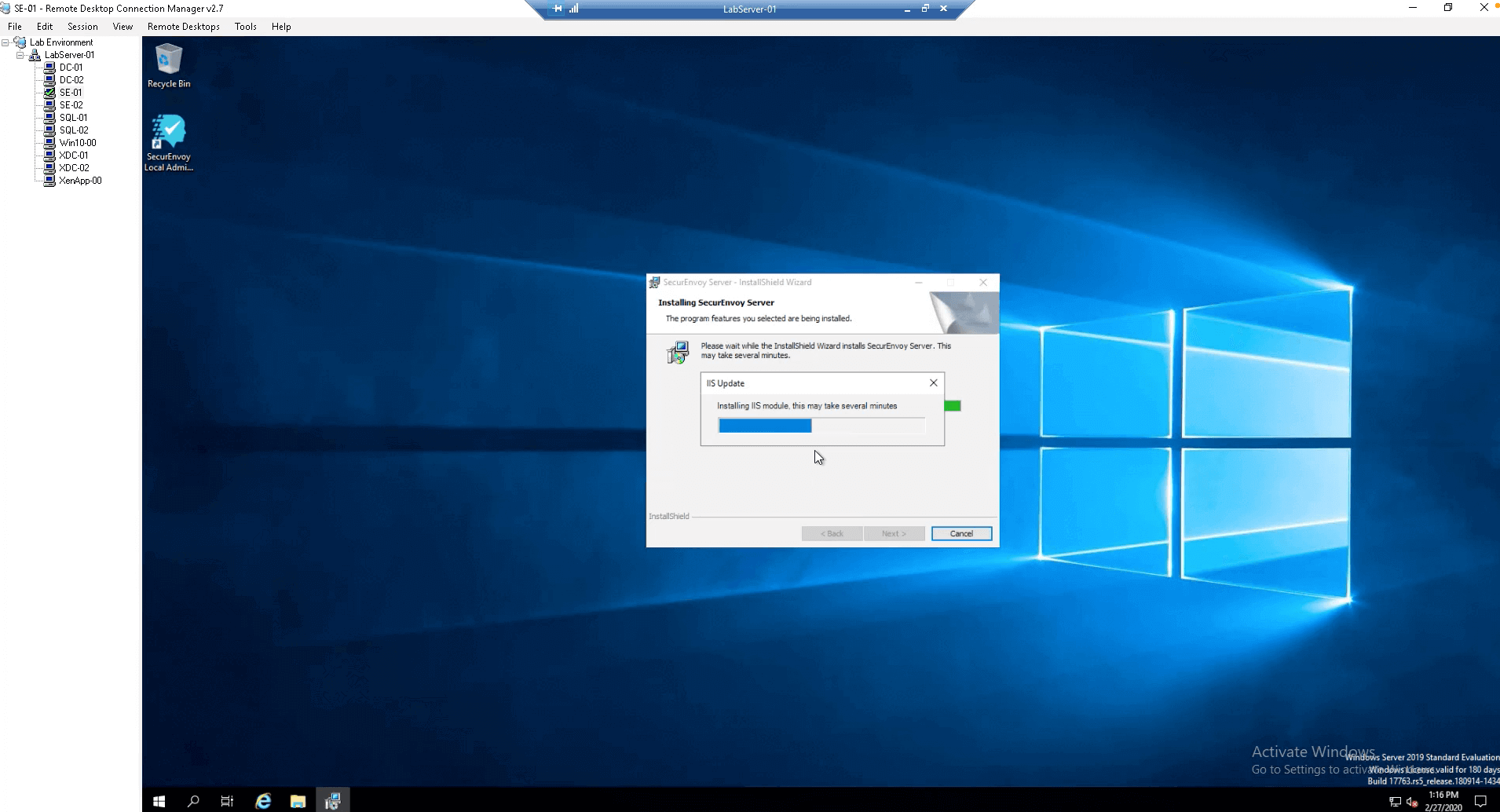
- Guías de Integración >
Visite nuestra área de soporte para ver más útiles recursos técnicos
- Seminarios Web recientes >
En vivo y en diferido – Utilícelo como crea conveniente
- Blog para capacitación industrial >
Tratando desafíos, amenazas y tecnologías en el marco industrial. Considerando técnicas y soluciones para avanzar efectivamente.
- Nuevos vídeos >
-
Asociaciones Convertirse en socio >
SecurEnvoy emplea socios especializados a nivel global. De esta forma entregamos soluciones enfocadas a nuestros clientes y aseguramos una relación directa con nuestros socios tecnológicos.
- Integraciones de socios tecnológicos >
Nuestra SecurIdentity Suite se integra con muchas de las tecnologías y empresas punteras
- Localizar socios de SecurEnvoy >
Localice un socio autorizado de SecurEnvoy para una integración perfecta en su compañía
- Convertirse en socio >
Cerca de 20 años adoptando consorcios
- Seminarios Web para socios >
- Portal socio >
Acceda a recursos de su portal de socio
- Registro de acuerdos >
Para socios distribuidores de SecurEnvoy
- Integraciones de socios tecnológicos >
-
Soporte Soporte SecurEnvoy >
Nuestro modelo de soporte está creado con nuestros clientes en mente , establecer relaciones estrechas y ofreciendo un soporte efective es vital para nuestro negocio. Nuestro soporte recibe un feedback de 4.2 sobre 5 con un 80% de nuestros clientes no necesitando ningún tipo de soporte, pero no dude en contactarnos.
-
Empresa Acerca de SecurEnvoy >
Cerca de 20 años encabezando innovación. Progresión de SecurIdentity & Protection Suite. Parte de Shearwater Group plc.
- Únete a SecurEnvoy >
Forma parte del equipo de SecurEnvoy , dónde la innovación y nuestros clientes son nuestro foco.
- Prensa >
Comunicados de prensa y artículos más recientes
- Blog capacitación industrial >
Tratando temas como desafíos , amenazas y tecnologías. Considerando soluciones y técnicas para avanzar efectivamente.
Blogs Recientes (En inglés )
+ What is Passwordless Authentication security and why are organisations implementing it? >
- Únete a SecurEnvoy >